Search results for tag #linux
There’s something special about a clean terminal and a fresh coffee on a system that just works the way you want it to.
Spent way too much time hopping distros, but Arch + KDE is where I finally settled. It’s nice not having to fight your own OS for once.
Anyone else rocking a custom setup? Drop a neofetch or a screenshot below, I’m looking for some fresh inspiration.
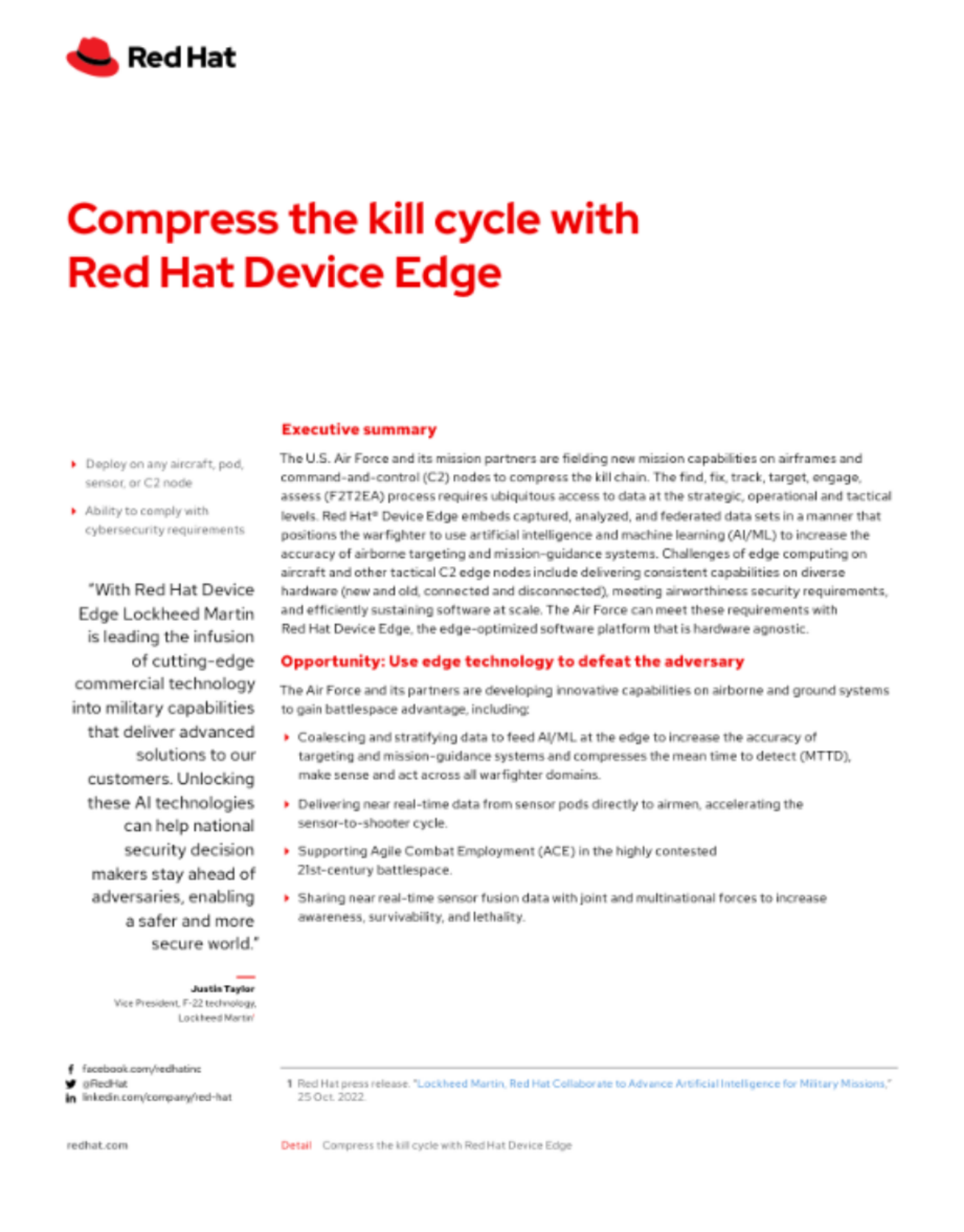
🐧💿 #RedHat is the top #Linux #distro for #genocide.
https://web.archive.org/web/20260402155236/https://www.redhat.com/rhdc/managed-files/ve-compress-the-kill-cycle-detail-693397pr-202402-en_3.pdf
#CompressTheKillCycle #IBM #RedHatDeviceEdge #LockheedMartin #AI #USAirForce #warfighter #lethality #LinuxDistribution
Davide Ornaghi and Giuseppe Caruso found a very interesting bug in #Linux's in-kernel Samba3 server from 6.12 to 6.19.x. Essentially, from the commit message and #CVE description:
> Currently, ksmbd does not verify if the user attempting to reconnect to a durable handle is the same user who originally opened the file. This allows any authenticated user to hijack an orphaned durable handle by predicting or brute-forcing the persistent ID.
Very interesting stuff! The kernel let's users resume their connection to an open file even after WiFi drops (durable handle), and a bug in this code let another authenticated user become this WiFi-dropped user, letting the hijacker access all files.
https://github.com/TurtleARM/CVE-2026-31717-KSMBD-Exploit
CVE-2026-31717
@mrmasterkeyboard @f4grx @projectanchorage yeah, I got build times of ~ 15min on an i7-6700k for #linux-6.6.6 @ i486 and a stripped-down version of #toybox.
Right now I try to replace #SYSLINUX with #mlb on @OS1337 so I don't waste >200 kB just on a #bootloader when all I have is 1440 kB…
It's jist that I don't get the quietness and time to do this properly…
@mrmasterkeyboard @f4grx @projectanchorage *pressing thumbs*
In terms of userland, you may want to take a look at #toybox when it comes to smol, tho that requires at least #i486 so propably not an option for you.
- Not shure if i486 is a hard requirement or if @landley didn't bother with #i386 as it was #EoL'd by #Linux.
@landley @mrmasterkeyboard @f4grx @projectanchorage good to know. I guess #i386 prebuilds are not done due to lack of demand, which is understandable given mainline #linux axed that before #toybox got released.
Your LG and Samsung TV's are, basically, spying on you
https://www.consumerreports.org/electronics/privacy/how-to-turn-off-smart-tv-snooping-features-a4840102036/
https://www.lg.com/global/newsroom/news/home-entertainment/lg-smart-tvs-get-a-new-acr-solution-legacy-technology-replaced-by-lg-ads-solutions/
Ad-free and privacy-respecting version of this video: https://tux-edu.tv/w/phzcXJWeLnVkeHxqGCzPcw
Make sure to motivate me for more content by, at least, liking the video and leaving a comment. It means a lot to me. Sharing this video with your friends is most welcome as is following this channel!
You can support the work financially here:
- https://ko-fi.com/darth
Social links:
- My webpage: https://linuxrenaissance.com
- I am fairly active on Mastodon: https://silversword.online/@darth
- My Matrix chat space: https://matrix.to/#/!LWfgnmBeCrpLbcWIlr:matrix.org
- My PeerTube channel: https://tux-edu.tv/c/lxr
- My YouTube chanel: https://youtube.com/@LinuxRenaissance
- My Odysee channel: https://odysee.com/@LinuxRenaissance:1
This video was edited with Kdenlive.
Intro / outro music is borrowed with permission from H0ffman:
https://soundcloud.com/h0ffman/sets/protracker-amiga
If you were thinking about switching from Debian/a Debian derivative, because you wanted to get away from LLMs/systemd, what would you switch to, particularly if you wanted the least amount of hassle? Other answers/reasons in comments if you like!
| Debian but with OpenRc: | 0 |
| Alpine Linux: | 0 |
| Chimera Linux: | 0 |
| OpenBSd: | 0 |
🚨 PH4NTXM News!
PH4NTXM has officially entered its most stable state so far.
After extensive restructuring, cleanup, testing, and internal improvements, the project has moved beyond its experimental phase and is now operating in a far more mature and reliable form.
For long-time followers of the project:
thank you for sticking around during the early development and experimental stages. The repository has evolved significantly since then.
For newcomers discovering PH4NTXM for the first time:
welcome. Now is a great time to explore the project, test it, review the architecture, and follow its development.
The repository now includes:
• improved structure
• cleaner documentation
• refined operational flow
• better modularity
• more consistent behavior across components
• extensive technical documentation
PH4NTXM now ships with more than 60 dedicated documentation files covering the environment in depth, explaining components, architecture, operational flow, usage, deployment, and system behavior step-by-step.
The goal is not only to provide tooling, but also to make the project understandable, transparent, and accessible to the open-source community.
PH4NTXM remains fully open-source and community-driven.
Feedback, testing, discussions, issue reports, and contributions are always welcome from anyone interested in privacy, operational security, hardened Linux environments, and defensive tooling.
The experimental era is over.
PH4NTXM is now entering its stable phase.
#ph4ntxm #linux #debian #os #live #privacy #security #opsec #infosec #research #tech #technology
Let's Encrypt just stopped the issuance of certificates after an "incident":
https://letsencrypt.status.io/pages/incident/55957a99e800baa4470002da/69fe2d6698ca07050eb4b1b3
If anyone encounters issues today with failed certificate renewals: It's probably not your setup.
"Another major Linux security flaw revealed — 'Dirty Frag' allows root on all major distros, with no patch or fix available yet"
"A researcher shared their findings with Linux distro maintainers, but leaked before a patch was built."
----------------
🎥 Video
===================
Opening: The announcement describes a free webinar titled “Digital Forensics: Basic Linux Analysis After Data Exfiltration — Hackers Arise” scheduled for February 13, 2026. The core narrative emphasizes that intrusions often present as an adversary already resident in an environment rather than beginning with an obvious malware drop.
Technical Details: The event framing indicates a focus on post-exfiltration Linux analysis. Topics implied by the title and tagline include identification of forensic artifacts left after data exfiltration, methods to examine Linux hosts for traces of adversary activity, and investigator-centric techniques for reconstructing actions when initial compromise is not observable. The announcement explicitly centers on the concept that adversaries can be present before any exploit or payload execution.
Analysis: Framing investigations around the “adversary-inside” perspective shifts attention to persistence mechanisms, lateral movement artifacts, evidence of data staging and egress, and gaps in audit/visibility that enable prolonged dwell time. While the announcement does not list IoCs or specific tools, it signals an emphasis on host-level evidence collection and reasoning about timelines and artifact correlation on Linux systems.
Detection: Although the source does not provide detection signatures, the webinar’s scope suggests discussion of detection opportunities such as anomalous outbound connections, unusual file access patterns, unexpected scheduled jobs or services, and forensic indicators in system logs and memory snapshots.
Implications for IR practitioners: The stated narrative reinforces the need to treat post-exfiltration analysis as a distinct investigative discipline with its own priorities—establishing a timeline, locating exfiltration vectors, and validating whether data staging or covert channels were used.
Limitations: The announcement is a webinar summary and does not publish technical IoCs, ATT&CK IDs, or tooling details. Attendees should expect conceptual framing and case-oriented walkthroughs rather than a repository of signatures.
References: Event title and date as published by the organizers: “Digital Forensics: Basic Linux Analysis After Data Exfiltration — Hackers Arise”, Feb 13, 2026.
🔹 digitalforensics #linux #incidentresponse #dataexfiltration #forensics
🔗 Source: https://hackers-arise.com/digital-forensics-basic-linux-analysis-after-data-exfiltration/
[$] Forgejo "carrot disclosure" raises security questions https://lwn.net/Articles/1071499/ #tech #linux
The main complaint about the Linux on the desktop was how ugly and inconsistent the GUI applications looked.
Looks like Mac and Windows devs are doing their best to have their platforms to be on par with Linux.
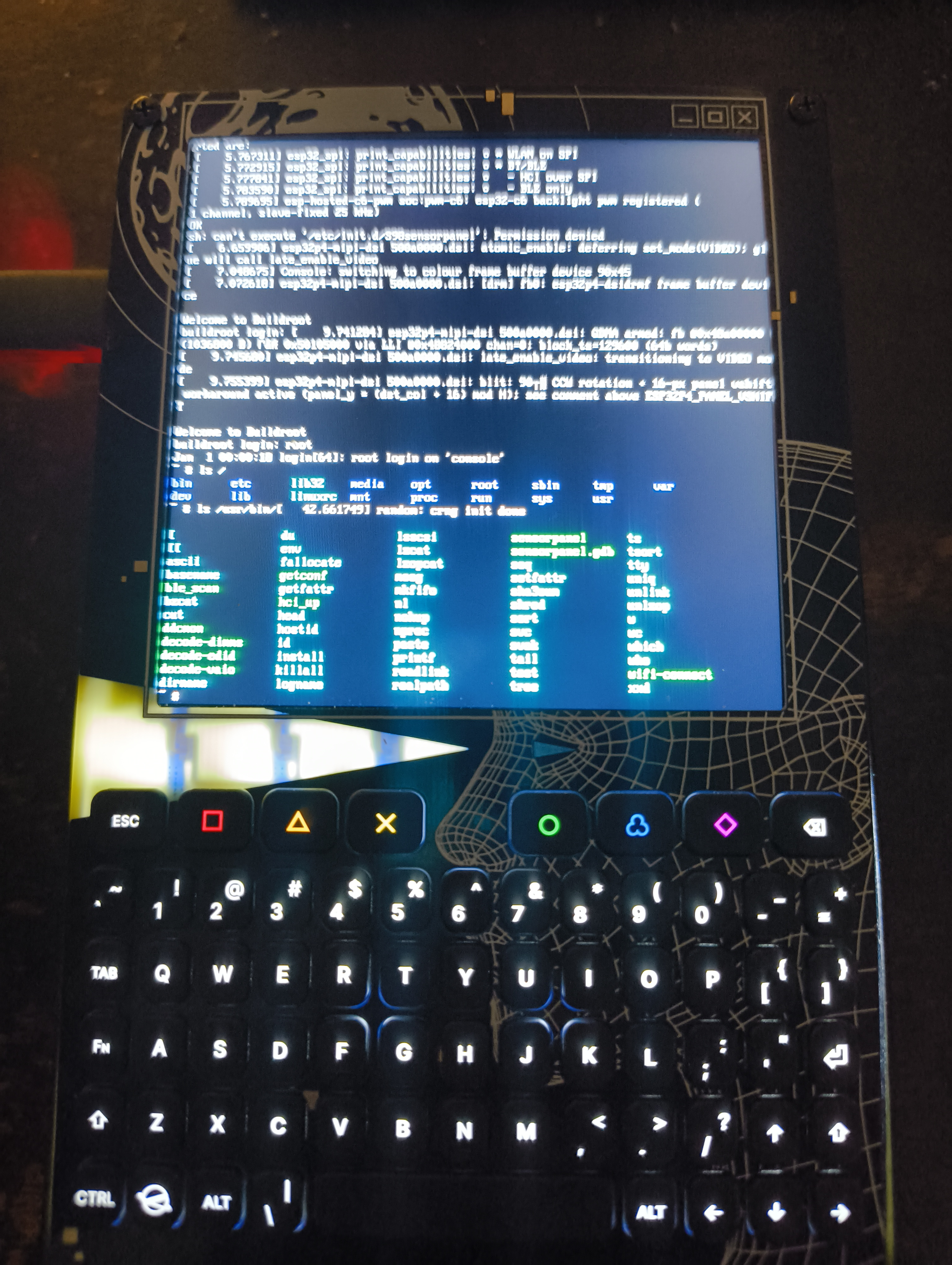
Holy Shit, this is awesome! #Linux on the #WHY2025 badge.
https://github.com/mrbreaker/why2025-linux
Screenshot from the GitHub
Something I've complained about when people deploy Linux kernel based OS's is so few people ever tune or customizes their kernels or their base distro's.
This used to be something old school sysadmins would do, as part of the basic security hygiene practice - "If you don't need it, don't include it", which applies to daemons , services and packages.
Kernel compilation is something that rarely seems to happen too..
Do you have hardware encryption capabilities you want things like wolfssl to use? Then sure use #AF_ALG . Anything else? Highly unlikely.
Are you running OpenSwan, or some other VPN or tunneling software that uses encapsulating tunnel options? No? Probably don't need ESP4/ESP6 modules.
Easy for me to call out sure, and i'm taking myself to task as well, since really at work, they don't want people deep diving and compiling kernels in many places. "Trust the vendor" where many mgmt types don't get it or care. "Apt/DNF update and carry on".
Funny because this the antithesis of their "resist patches, and updates" attitude towards software.
The number of mongodb 3.x db's out there because the dev hasn't updated the driver, or the number of npm warnings "this is vulnerable, don't use this" that are ignored are high.
#Dirty #Frag: A new #Linux privilege escalation vulnerability is already in the wild
https://securityaffairs.com/191847/hacking/dirty-frag-a-new-linux-privilege-escalation-vulnerability-is-already-in-the-wild.html
#securityaffairs #hacking
#Linux kernel exploit mitigation:
rm -rf /boot /lib/modules && reboot
Will mitigate all exploits, not just #DirtyFrag 🧐☝️
Nouveaux kernels stables : 7.0.5 / 6.18.28 / 6.12.87 / 6.6.138
Ils embarquent un fix partiel pour #DirtyFrag (CVE-2026-43284) et Copy Fail 2.
Partiel, car Greg Kroah-Hartman a confirmé qu'un second patch est encore en développement et n'a pas encore été mergé.
La mitigation par blacklist des modules reste donc recommandée en attendant.
👇
https://lwn.net/Articles/1071775/
variante peu sympa 👀
"Unprivileged Linux LPE via xfrm ESP-in-UDP MSG_SPLICE_PAGES no-COW fast path. Page-cache write into any readable file. Overwrites a nologin line in /etc/passwd with sick::0:0:...:/:/bin/bash and sus into it. Same class as Copy Fail (CVE-2026-31431), different subsystem."
⬇️
https://github.com/0xdeadbeefnetwork/Copy_Fail2-Electric_Boogaloo
Hm, neuerdings reagiert mein PC während der Boot-Phase, einschließlich GRUB, nicht mehr auf die Funkmaus oder Funktastatur.
Erst, wenn der Anmeldebildschirm von Kubuntu auftaucht, funktionieren Maus und Tastatur.
Bin mir nicht bewusst, im BIOS irgendetwas geändert zu haben.
Kennt jemensch das Phänomen?
Kubuntu 25.10
[VULN] ⚠️ "Dirty Frag : cette faille zero-day donne les droits root sur Linux"
"Dirty Frag, c’est le nom de la nouvelle faille de sécurité critique qui affecte les machines Linux. Cette faille zero-day est similaire à Copy Fail puisqu’elle permet une élévation de privilèges en tant que root. Voici l’essentiel à savoir sur cette menace potentielle.
La vulnérabilité Dirty Frag a été découverte par le chercheur Hyunwoo Kim, qui avait initialement planifié une divulgation coordonnée pour le 12 mai 2026. Cependant, quelqu’un est parvenu à détecter des informations relatives à cette vulnérabilité, et donc tout a été publié en avance ce jeudi 7 mai 2026."
Hyunwoo Kim a pris la décision de publier tous les détails, notamment pour alerter la communauté : “Parce que l’embargo a été rompu, aucun correctif ni CVE n’existe pour ces vulnérabilités. Après consultation avec les mainteneurs de linux-distros@vs.openwall.org, et à la demande des mainteneurs, je publie publiquement ce document Dirty Frag.”."
👇
https://www.it-connect.fr/dirty-frag-cette-faille-zero-day-donne-les-droits-root-sur-linux/
⬇️
https://www.openwall.com/lists/oss-security/2026/05/07/8
👇
https://github.com/V4bel/dirtyfrag/blob/master/assets/write-up.md
Harmaa sydän -ongelma (ratkaistu jo aiemmin)
Pari kuukautta ihmettelin miksi tykkäämäni Mastodon postauksen sydän on aina harmaa, paitsi silloin kun refreshaan sivun.
Ärsytti nyt tämä pikkuvika niin paljon, että oli pakko selvittää mikä homma. Vaikeinta oli lähteä etsimään oikeasta paikasta juurisyytä. Ensin epäilin, että @rolle n BirdUI:ssa on joku CSS-ongelma. Rolle sanoi ettei pitäisi olla mitään ongelmaa. Mun sydänongelma (ei sentään oma elin  ) koski nimenomaan CachyOSia, muilla käyttöjärjestelmissä näkyy oikein selaimesta riippumatta.
) koski nimenomaan CachyOSia, muilla käyttöjärjestelmissä näkyy oikein selaimesta riippumatta.
Nyt vasta hoksasin tarkistaa KDE Plasman asetukset tarkemmin ja sieltä löytyikin syypää.
Ulkoasut ja Teemat > Animoinnit > Animoinnin nopeus 'välitön'. Välitön tila laukaisi tämän ongelman. Säädin animoinnin nyt hitaammaksi ja heti ratkesi ongelma. 'Välitön' aiheutti sydämen animoinnin poistamisen, kun se on aktiivisena. Kyseisen asetuksen lisäinfossa mainitaan, että ongelma saattaa koskea nimenomaan GTK sovelluksia ja animointi ei toimi niissä oikein tässä tilassa.
PS. Tämä oli muistiinpano itselleni. 🤓
DirtyFrag: Linux LPE
This #exploit works by chaining the xfrm-ESP Page-Cache Write vulnerability and the RxRPC Page-Cache Write vulnerability.
“Dirty Frag”: Linux flaws grant root access
Further vulnerabilities named “Dirty Frag” enable privilege escalation. All distributions are reportedly affected.
„Dirty Frag“: Linux-Lücken verschaffen root-Rechte
Weitere Lücken mit dem Namen „Dirty Frag“ ermöglichen die Rechteausweitung. Betroffen sind wohl alle Distributionen.
Ubuntu’s X account was briefly compromised to promote a fake AI crypto project using cloned branding, Solana tags, and a deceptive Ubuntu-style domain ⚠️
The phishing thread followed days of DDoS attacks on Canonical services 🔐
🔗 https://itsfoss.com/news/ubuntu-twitter-compromised/
#TechNews #Ubuntu #Canonical #Linux #Cybersecurity #Phishing #DDoS #OpenSource #Privacy #Infosec #Solana #Blockchain #FOSS #Transparency #X #AI #ArtificialIntelligence #Crypto #Cryptocurrency
So I'm curious, #Musicians
There are now legions of people using #Linux for recording, synthesis, processing, etc - it's a full-on cottage industry at this point.
There are also a large number of Music Professionals using #BSD, but they call it MacOS.
But what I'm curious about, what is the state of Music Production on #FreeBSD and other non-Apple BSD.
I will not be surprised if it turns there are none, nor will I be surprised if it turns out that there is a tiny community of elite DSP nerds making high-end products with it.
"fdisk Cheatsheet"
"Quick reference for fdisk commands: list disks, create partition tables, add partitions, change partition types, write changes, and quit safely"
Dirty Frag: Universal Linux LPE https://www.openwall.com/lists/oss-security/2026/05/07/8
This is a report on "Dirty Frag", a universal LPE that allows obtaining root privileges on all major distributions. This vulnerability has a similar impact to the previous Copy Fail.
Oh good, another high-severity #Linux #security vulnerability that somebody botched the disclosure of, turning it into a high-severity zero-day.
Because #CopyFail wasn't bad enough. Now we've got #DirtyFrag too.
Can #cybersecurity people please stop botching vulnerability disclosure? Thanks.
heute für meinen Vater ein Acer Aspire 1 mit einem LinuxMint installiert. Ich habe ihm KDE Plasma installiert. Dabei ist mir aufgefallen, dass die Angebotenen Meta Pakete von KDE nicht gut zusammengestellt sind. Sogar bei kde-full - fehlte so einiges, dass man nachinstallieren musste.
Dirty Frag: a zero-day universal Linux LPE https://lwn.net/Articles/1071719/ #tech #linux
RE: https://infosec.exchange/@harrysintonen/116535053646996124
> Due to external factors, the embargo has been broken, so no patch exists for any distribution.
To mitigate, disable rxrpc, esp4 and esp6
Hatte dann endlich mal die Zeit, meinen public server mit WireGuard zu versehen um anschließend ssh (mit agressivem fail2ban gesichert) von extern abzuschalten.
Hey there #linux users, what #distro are you using and why? I used to run #archlinux, then #fedora. Currently on #ubuntu for the proprietary Nvidia support, though I generally prefer the vanilla gnome experience.
Notta saapa nähdä montako päivää tässä menee totutellessa, tahi tuleeko meille nyt sittenkin uusi tietokone kotiin. Harmi, että olen itse treeniohjelman vuoksi jumissa Applessa, sitä kun ei Linuxille saa.
En kyllä tiedä saisiko edes millään Linux versiolla vaihdetuksi tilistä toiseen pelkän lepotilan kautta, kirjautumatta joka välissä ulos.
Niri bringt frischen Wind auf den #Linux-Desktop: Der Tiling-Wayland-Compositor reiht Fenster wie Perlen auf eine Schnur und lässt schnell horizontal hindurchscrollen. Flinke Tastensteuerung, wenig Ballast und eine optionale Desktop-Shell machen aus Niri eine elegante Desktop-Alternative. Läuft bei mir jetzt seit einigen Wochen und gefällt mir sehr.
For my fellow #Linux friends: This is a small project, I have worked on.
It is a solar system animation, coded in rust, that runs in your terminal.
You'll find packages for your distro on GitHub. Nix users will find a flake and Arch users can install from the AUR.
#macos and #windows users can compile from source.
Link to the Repo: https://github.com/the-unknown/solarust







 decio
decio
